An IP (Internet Protocol) Address is largely how your computer or tool is identified on the net. Any laptop or device connected to the internet must be assigned a logical IP Address whether or not it’s from your ISP (Internet Service Provider) or your neighborhood router’s DHCP (Dynamic Host Configuration Protocol) server. The Info Blog
You can think about an IP Address like an automobile’s license plate. Every vehicle driving on the road (legally) has a registration code registered to the local DMV. The registration code is like the car’s identity card, which allows a person (typically a cop) to run the plate and find all types of records, including the automobile’s proprietor to which the license plate is registered. An IP Address works in the same manner. Every computer surfing the internet has to have a few forms of figuring out IP Address, whether or not it’s an IP assigned to the actual computer, the router the computer is connected to, or the proxy server the PC is connecting with. This identifies a computer on the net as a registration code that identifies a vehicle on the street.
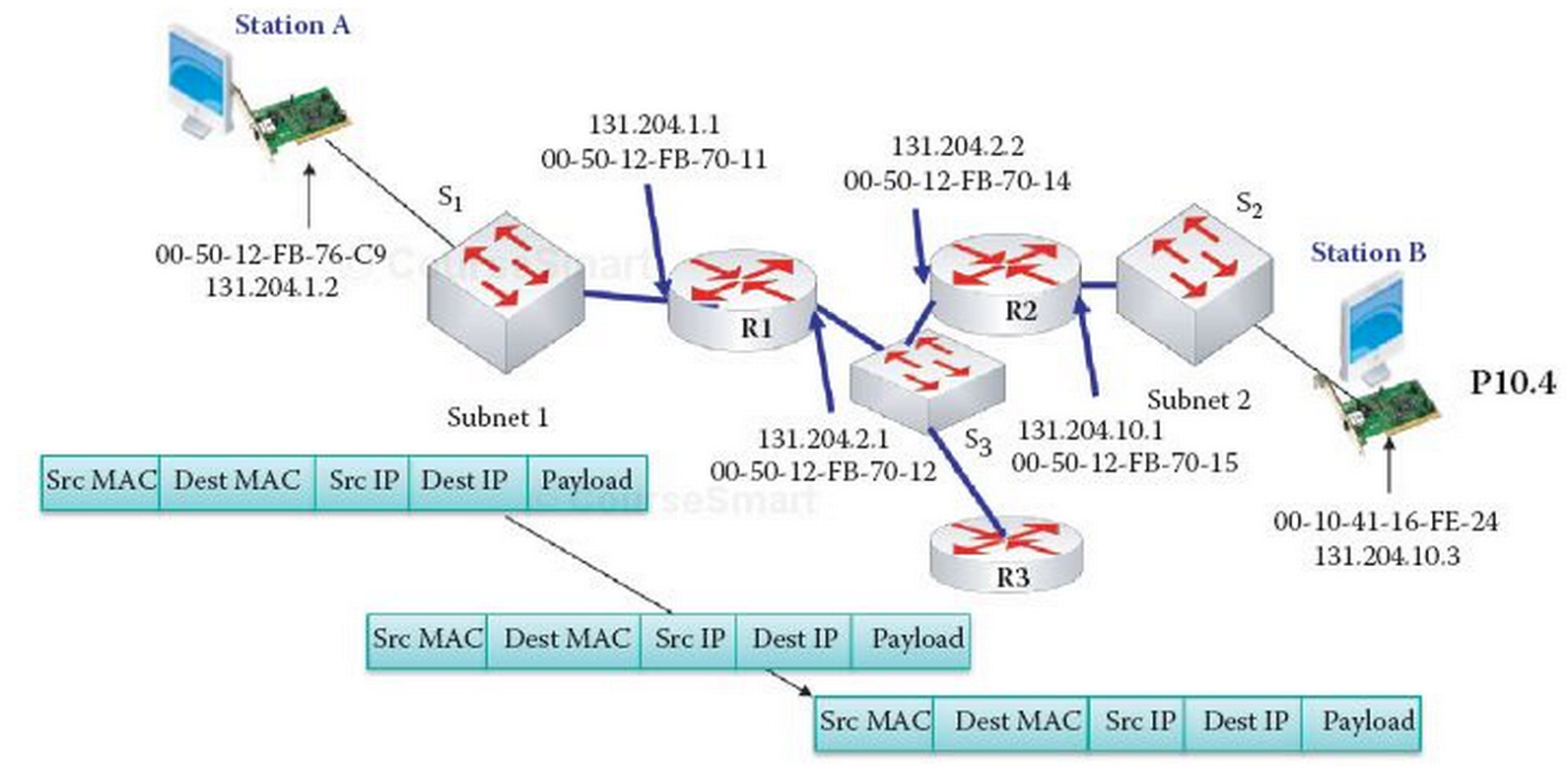
A MAC (Media Access Control) Address, however, is the physical address of the NIC (Network Interface Cards) on your computer (something like a serial quantity). Along with Ethernet, the MAC deal uniquely identifies every node (computing device/laptop) for unique packet shipping on broadcast networks. If you revel in analogies, you can evaluate the NIC’s MAC cope with a vehicle’s VIN quantity. The MAC identifies the physical networking hardware as an automobile’s VIN identifies a particular vehicle.
I picked a vehicle for my analogies to help readers remember that a dynamic IP Address can alternate just like a car’s registration code variety may be changed. But a MAC Address (beneath most instances) cannot be changed, similar to a vehicle’s VIN cannot be changed.
However, a static IP Address is an IP address that you preserve regularly and by no means changes (and typically should pay a charge for). A static IP is beneficial for people who run servers or any device where you need the IP address to stay the same constantly.
My name is Sergio Woods, and I’ve been analyzing computer systems for over seven years. I even have a superb deal of information in components from Internet Administration to software program programming to hardware and component installation. In my research, I understand that there are very fashionable matters even the maximum casual computer user needs to know how to preserve their laptop jogging at its top overall performance.
I want to proportion my understanding with anyone who wants to analyze the whole lot there’s to know about the most innovative entity in our society. I attempt to explain the entire lot in layman’s phrases without using technical jargon. Also, I’ve realized that various humans are charging humans an arm and a leg to provide a prevalent computer advocate, which isn’t worth that awful lot. Sometimes, humans want a little push within the proper path, and Computer Maintain.Com offers that push.
Mac’s key logger program (undercover agent software) is extensively developed and used in many aspects. But plainly, the majority don’t know what sort of key logger can help them to the utmost volume. The following examples will let you know precisely which one to buy.
Case 1: Your children usually take benefit of your operating and shopping time to apply your computer. But you by no means see the website records. They are quite young, so you must recognize what they may be doing at the computer in your absence.
Solution: Since you are the laptop administrator and have all permissions, you may set up a key logger software program for Mac on your laptop to tune your kids’ conduct online. Select a tool to record keystrokes, log Internet sites visited, and capture display screen photographs. Some professional ones may even record passwords.
Case 2: Your husband has been going out almost every night and occasionally got here domestic the following morning. He changed the admin password of his Mac to the only one you don t know. He has been impolite to you and refused to speak to you. He has appeared so unusual that you must recognize if he’s cheating on you.
Solution: It might be higher if you operate spy software that supports far-flung setup because you haven’t any bodily right of entry to your Mac. A Remote Mac Key logger is your desire. It might be better if the far off you will send logs to your email or FTP vicinity. Password safety is continually critical, so your husband cannot uninstall it.
READ ALSO:
- Windows 10 Home vs. Windows 10 Pro: What’s the Difference, and Which One Is for You?
- How To Fight The Rising Prices Showcased In Insurance News Year After Year
- Pandora, Mecca, and Mac: The intense spots of Australian retail
- Video Games and the Law: Sex, Violence, and Addiction
- What Is the Facebook Wall and the News Feed?












